Strengthening the mobile defense line of judicial supervision: Analysis of the military-grade security architecture of the ThinkRace device
The Data Fortress of Citizens' Privacy and Law Enforcement Dignity
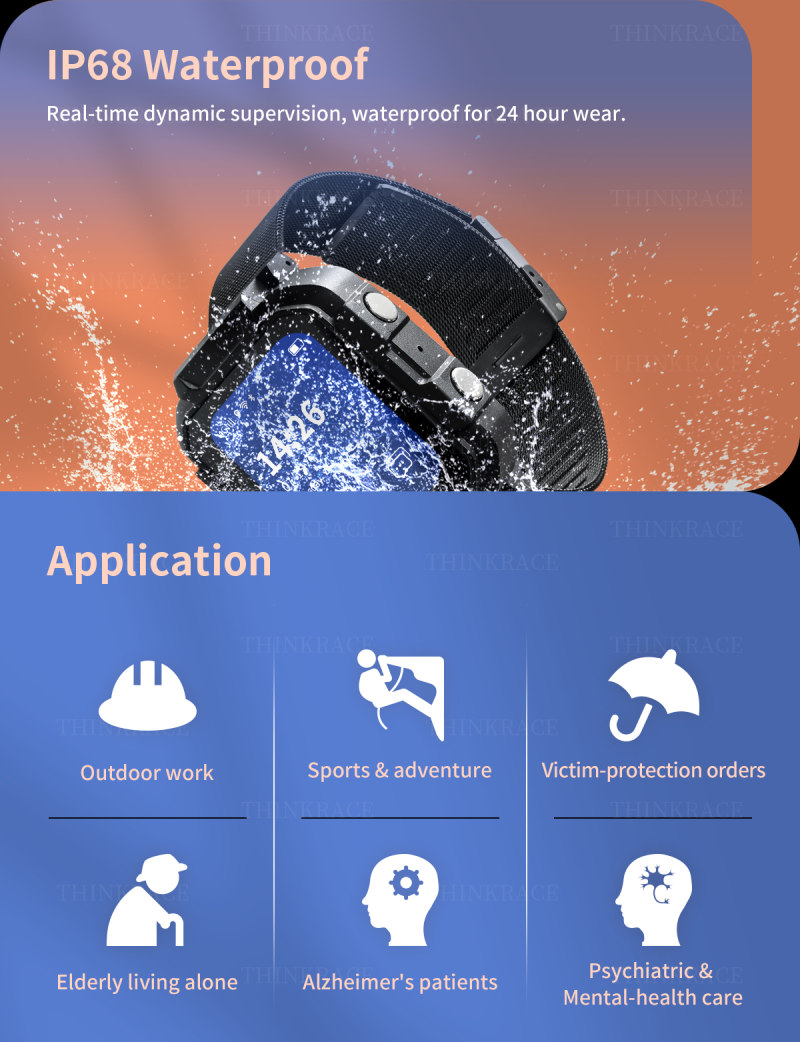
In scenarios such as judicial monitoring, community correction, and smart construction sites, intelligent wearable devices are not only positioning tools but also data fortresses that safeguard citizens’ privacy and uphold the dignity of law enforcement. The ThinkRace smart GPS watch, electronic handcuffs, and ankle cuffs series have recently completed a comprehensive upgrade of their security system from the terminal to the cloud. With military-grade encryption algorithms and transmission protocols, they have set a new security benchmark for the industry.

Core Encryption: Optimized for Mobile Devices - ChaCha20-Poly1305
Taking into account the characteristics of ARM architecture processors in wearable devices, all ThinkRace products incorporate the highest-level ChaCha20-Poly1305 encryption algorithm in the field of mobile security. Compared to the traditional AES-GCM algorithm, ChaCha20-Poly1305 has significant performance advantages on mobile devices: without relying on hardware acceleration (such as the AES-NI instruction set), its encryption and decryption speed can reach 3-4 times that of AES, significantly improving data throughput efficiency and reducing device power consumption, thereby extending battery life. This algorithm provides 256-bit encryption strength, and Poly1305, as an identity authentication algorithm, can provide confidentiality, integrity, and authenticity guarantees for data, effectively preventing man-in-the-middle attacks and data tampering.
Transmission Security: Dual Insurance of MQTT over TLS
At the network transmission layer, the ThinkRace devices adopt the lightweight and widely used MQTT protocol and enforce the use of the TLS secure transport layer protocol (supporting versions 1.2 and above). The low bandwidth consumption characteristic of MQTT is suitable for the real-time connection requirements of a large number of devices, while the addition of TLS provides an “encrypted tunnel” for the transmission pipeline. Through certificate verification and key negotiation during the TLS handshake process, all location data, vital sign information, and control instructions between the device and the server are transmitted in encrypted form, completely blocking link sniffing and illegal monitoring.
.jpg)
End-to-end closed loop: Anti-tampering hardware and API permission verification
Security is not limited to data transmission. The ThinkRace products continue the anti-tampering design at the physical level (such as hardened steel bands and anti-tampering alarm sensors), and on this basis, they have strengthened the security mechanism at the business layer. The device end supports two-way identity authentication to ensure that only legal servers can issue instructions; the server end provides RESTful APIs that have undergone strict permission verification, and the connection of third-party systems requires a secure authentication process using encryption keys and passwords to ensure that sensitive data can only be accessed by authorized users.
Military-grade security measures
From hardware anti-tampering to chip-level encryption using ChaCha20-Poly1305, to TLS transmission and API permission control, ThinkRace has established a deep-seated security defense system covering “end-point – network – cloud”, providing truly reliable military-grade security protection for judicial correction and industry supervision.

Introduce Our Products
ThinkRace, a leading manufacturer, specializes in comprehensive electronic monitoring solutions for the justice industry. We offer a range of products, including electronic restraints and smartwatches, designed to cater to the needs of offenders, law enforcement officers, and command personnel. Our hardware and software solutions are tailored to meet the critical business requirements of various stakeholders within the sector. Choose from our diverse product lineup to address your specific monitoring and security needs.